One Source of Truth for Every Party on the Deal.
Debtigo is the document infrastructure layer for modern enterprise work — version-controlled, permissioned, and built for the people and AI agents on your team.
Compliant
SOC II Type 2
100%
Encrypted at rest
Integrates with



The Problem
Your Documents Live in Three Disconnected Systems
Local drive, shared drive, data room. None of them talk to each other. Versions drift, permissions don't transfer, and every handoff is a leak waiting to happen.
Version Chaos
Your deal team is on CIM_Final_v9.pptx. Counsel has CIM_Final_v7. Nobody knows what's current, and reconciling versions burns hours every day.
Permission Gaps
Internal shared drives, external data rooms — two systems with no shared permission model. Every file transfer is a compliance risk.
Fragmented AI Workflows
Your team copy-pastes between Word, Excel, and a Claude chat because nothing connects. Agents can only see fragments, so people fill in the gaps by hand.
The Product
Built Like Git. Built for Deals.
Software teams solved this problem 30 years ago. They stopped emailing files and started committing them to a shared repository where every change is tracked, every contributor is scoped, and every version is recoverable.
Debtigo brings that model to enterprise documents.
One repository per deal, matter, or transaction. One authoritative version of every file. Internal teams, outside counsel, counterparties, and AI agents each work from a permissioned branch of the same source of truth. When the document changes, branches update. When a party leaves, their branch closes. Nothing forks into chaos. Nothing leaks.
How It Works
One Repo. Many Branches. One Source of Truth.
Three architectural primitives — borrowed from the version-control system that powers every modern software team — applied to the documents that close your deals.
One Version, Always
Hash-locked commits replace file copies. Every edit is tracked, timestamped, and cryptographically signed. The current version is the only version.
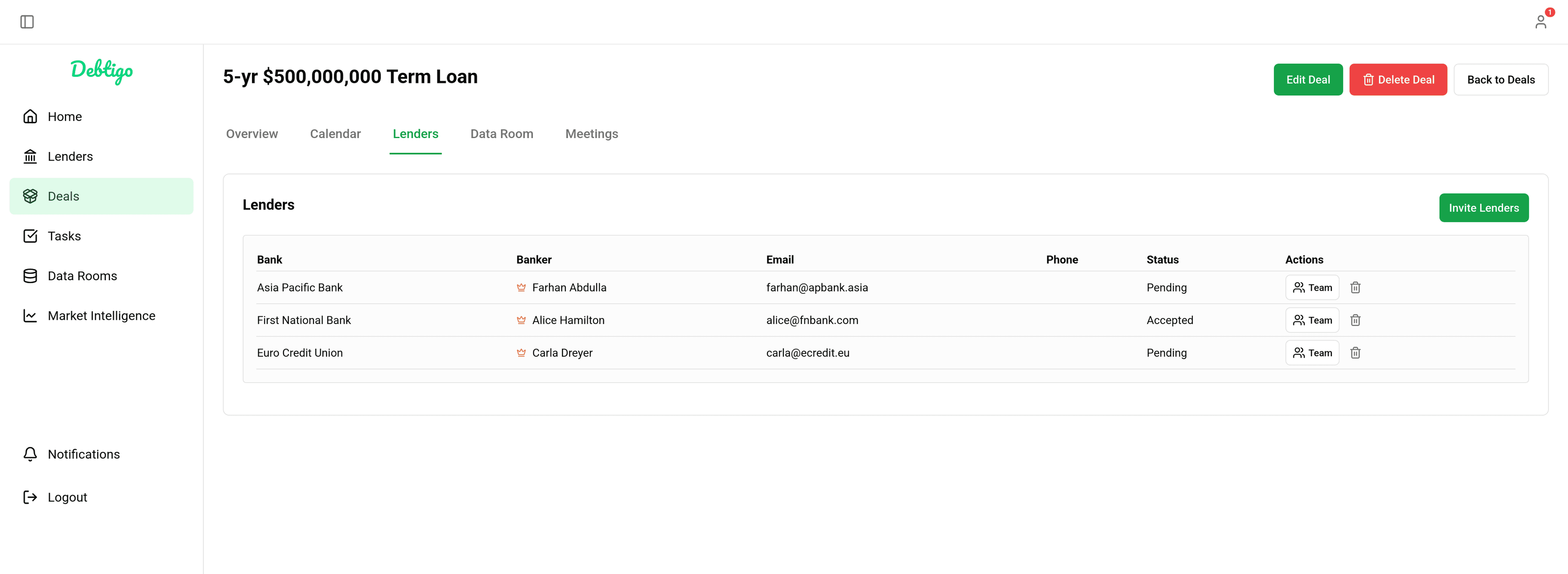
Permissioned Branches Replace Folder Sprawl
Each party — internal team, counsel, counterparty, agent — gets a scoped branch off main. Access is revocable in one click. Revoking a branch never touches the source.
Agent-Native From Day One
Your AI tools connect through a standard interface and operate inside the same permission model as your human team. Every action they take is attributed and auditable.
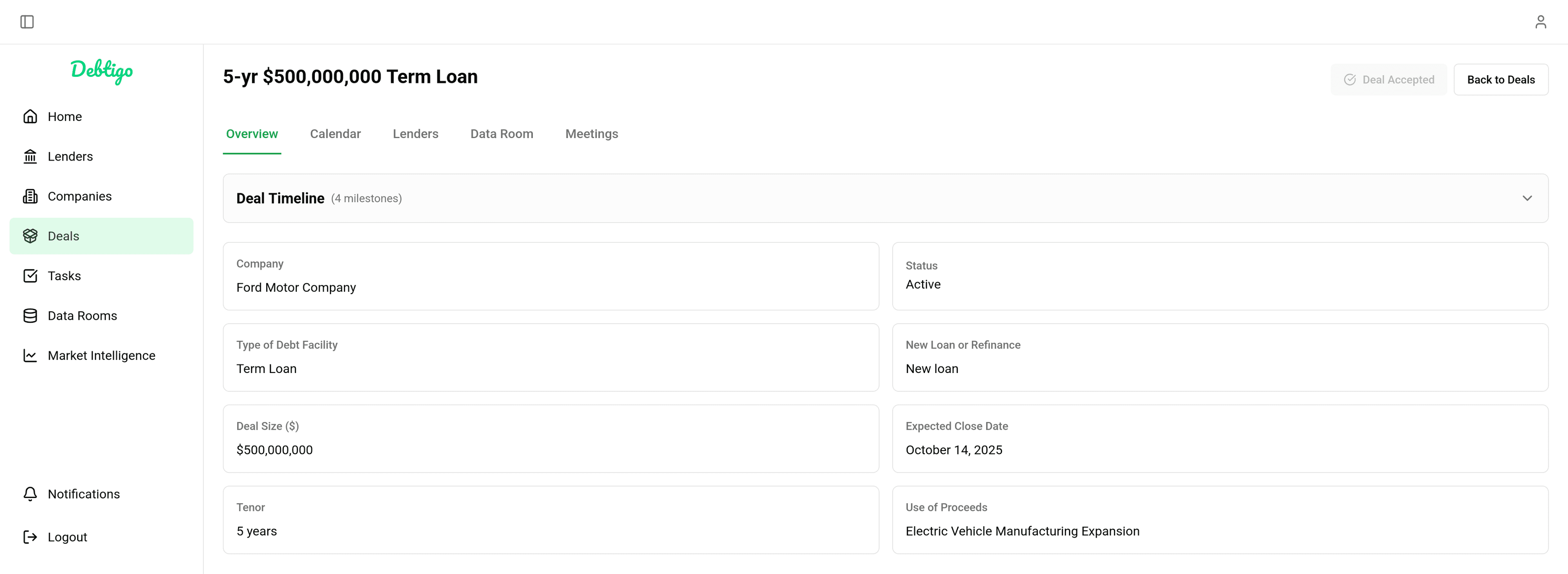
The Platform
Built for How Agents Actually Work
Every module is designed for organizations where AI agents are active participants in the deal workflow.
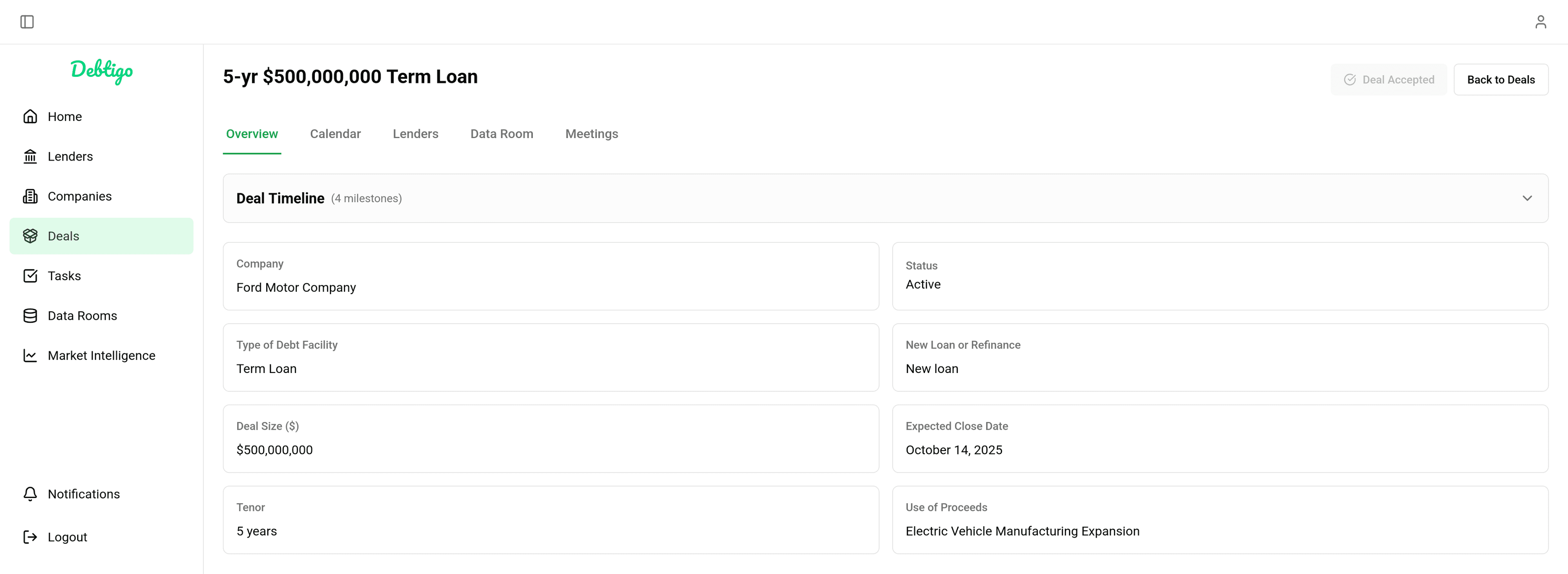
Document Repository
Structured Knowledge Across Every Deal
Organize documents by deal, counterparty, or matter — with metadata tagging that lets agents retrieve exactly what they need without scanning entire folders.
- Structured repositories with configurable organization
- Metadata tags that feed agents precise context instead of entire files
- Participant roles and scoped access at the file level
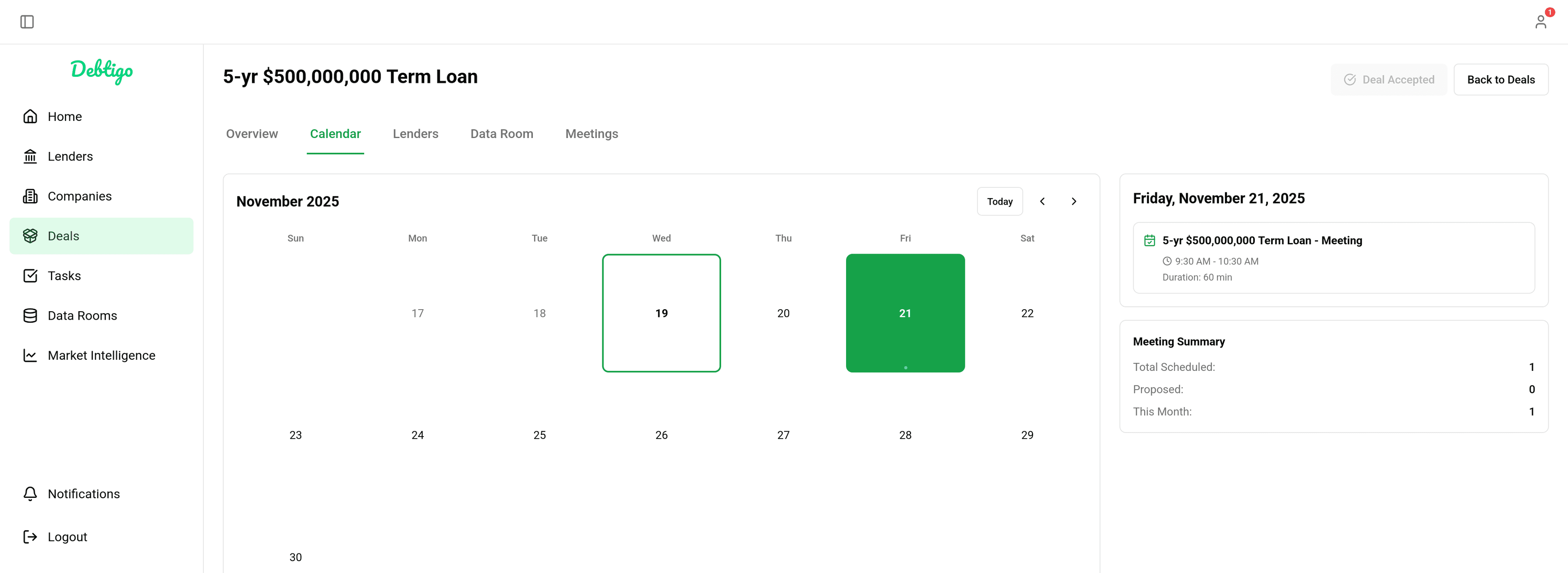
Counterparty Intelligence
One View of Every Participant, Every Interaction
Track engagement across across every person and agent
- Engagement tracking with full interaction history
- Access logs per counterparty and agent
- Notes and call logs tied to the deal record
- Follow-up queue and status visibility across all parties
Agent-Native Data Room
Always-On Access. Scoped. Audited. Revocable.
Give your AI agents a persistent MCP connection to your documents — with permissioned credentials that enforce 'Need to Know' at the agent level, not just the user level.
- Always-on MCP connection — no downloads or re-uploads
- Scoped agent credentials: permissioned, audited, revocable
- Bring Your Own Agents — works with Claude, Harvey, Rogo, Hebbia, and more
- Full audit trail of every human and agent access
Agent-Agnostic
Bring Your Own Agent
Debtigo is not tied to any single AI vendor. Connect Claude, Harvey, Rogo, Hebbia, Legora, or any agent your firm already uses — through a single MCP server that handles access, context, and auditability.
- One MCP server connection gives any agent structured, permissioned access to your deal data.
- Agents receive only the context they're authorized for — scoped per deal, per task, per firm.
- Switch or run multiple agents simultaneously without re-uploading documents or rebuilding workflows.
- Every agent action is logged, attributable, and exportable for compliance review.
MCP-native architecture. Works with any agent that supports the Model Context Protocol.
For Engineering Teams
Why CTOs Choose Debtigo Over Bolt-Ons
The architecture, the integrations, and the deployment options your security and infrastructure teams need to evaluate.
Git-native architecture with audit by default
Debtigo's data model is built from git primitives: content-addressed object storage, branch and merge semantics, and cryptographic commit history. Every commit is hashed, signed, and timestamped at write time, so the commit history is the audit log. There's no separate event stream to reconcile and no telemetry pipeline to maintain. Incumbents retrofit version control onto folder hierarchies. We rebuilt the substrate.
Agent-agnostic, AI-native
Debtigo exposes a standard Model Context Protocol (MCP) interface with pre-built connectors for Claude, OpenAI, Gemini, Rogo, Harvey, and Copilot. Any agent — including your internal model — connects with a single credential and operates within branch-scoped permissions. Every action by an agent is attributed in the same audit trail as a human commit.
Deploy Where Your Data Has to Live
For institutions with the strictest data-residency requirements, Debtigo on-prem pairs with a locally hosted model over the same MCP interface. The entire AI-assisted document workflow stays inside your perimeter. No external API calls. No exceptions.
Cloud (SaaS)
Debtigo-hosted, SOC 2 Type II. Fastest path to production.
Private VPC
Deploy into your own AWS, Azure, or GCP account. Data never leaves your cloud boundary.
On-Premises
Full on-prem deployment for air-gapped or sovereignty-bound environments.
Security & Compliance
Enterprise-Grade Security, By Design
Every document encrypted. Every action logged. Every participant verified.
AES-256 Encryption
All files and documents encrypted at rest and in transit. No plaintext data in storage.
Role-Based Access Control
Deal-level permissions ensure only authorized participants can see sensitive information.
Full Audit Trail
Every action — view, download, edit, approve — is logged, timestamped, and exportable.
SOC 2 Type II Ready
Security controls aligned to enterprise and institutional standards for compliance teams.
SSO / SAML Support
Integrate Debtigo with your organization's existing identity provider and access policies.
Data Residency Options
Control where your data is stored and processed. Available on Enterprise plans.
The Substrate for Document-Driven Work
If your team writes the documents that close the deals, defend the cases, or audit the books — Debtigo is the layer underneath.